Machine Learning Is Becoming a Must in Data Center Network Security
The volume of data traveling on networks and sophistication of attack tools are outpacing human experts’ capabilities.
August 14, 2018
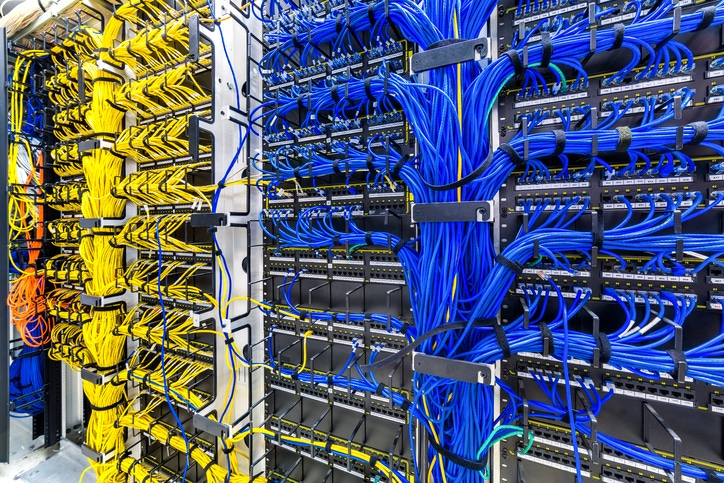
Data center networks are getting faster, larger, and ever more difficult to protect.
The amount of data traveling on them is outgrowing what humans can monitor manually. This is while growth in the number of qualified security professionals isn’t keeping up with demand.
It's bad enough when attackers use a brand-new attack vector to break in. It’s doubly painful when they use a known approach, and the security team doesn't pick up on it because it's swamped.
The attackers’ arsenal is getting more powerful. Availability of open source AI tools means they can deploy more sophisticated and damaging attacks faster than ever before.
Meanwhile, breaches are getting increasingly costly for the victims. For a smaller company, a high-profile loss of sensitive data or a ransomware attack that wipes out customer files can be a business-ending event.
Enhancing security capabilities with machine learning can not only help, experts say, it is becoming necessary.
Data center operators that “don't employ AI and machine learning to power behavioral-based security through automation, especially in the response and remediation of attacks, will leave themselves vulnerable by not keeping pace with the evolution of threat technology," Migo Kedem, director of product management at SentinelOne, a security firm based in Mountain View, California.
Security vendors are adding Artificial Intelligence and machine learning to their products to better detect threats, help companies automate their responses, and aid with forensic analysis of attacks.
Threat Detection
The three main machine learning techniques used for threat detection are classification, anomaly detection, and risk scoring.
For example, if there's a large collection of known malicious behaviors and a collection of known good behaviors, a machine learning system can be trained to sort new behaviors between those two categories.
This technique is currently used to improve malware detection – for example, by training the systems on examples of good software and malware to distinguish between the two.
With anomaly detection, a system learns what typical behaviors are on a network and looks for anything unusual.
Data center networks are particularly well-positioned to take advantage of anomaly-detection techniques, Debabrata Dash, co-founder at Awake Security, said.
"A data center network is typically well-controlled and automated through DevOps," he said. "Given this environment, activities that are out of the normal and detectable by machine learning are typically more security-relevant than a general enterprise environment."
Classification and anomaly detection can produce many potential threats. Risk-scoring techniques can sort them, so security staff can prioritize the ones likely to do most damage.
Risk scoring isn't just useful in identifying potential threats but also for finding weaknesses in a network and recommending which ones need to be fixed first.
That starts with having a good understanding of what devices, applications, and users are on the network, and whether everything is configured correctly and fully patched. This isn't as simple as it sounds, since both networks and risks can change quickly, and the number of things that need to be fixed can quickly exceed the time available.
Machine learning can help scale human expertise in analysis of network state and behavior, Gaurav Banga, founder and CEO of the security firm Balbix, said. It can also help evaluate whether the security controls in place are adequate and properly calibrated to defend against current treats.
Gartner calls this "risk-aware vulnerability management."
The most advanced products in this category can also assess the business risk of each possible vulnerability and suggest fixes.
ML-Aided Forensics
When a security professional is investigating an incident, pulling in logs from disparate systems and scanning them for relevant information takes time.
Machine learning-powered forensics streamlines this process by immediately pulling the data they will most likely want to see.
Response Automation
Once a threat is identified, the faster the mitigation the smaller the damage.
Automating some of the response can reduce reaction time and free up the security team to focus on more challenging problems. But creating automation scripts is itself time-consuming.
The hope is that, with AI, the systems will train on history of incident responses at a company and make recommendations for actions.
Recommendations that are the least risky while offering the most value can be carried out automatically, while the others are presented to human analysts for approval.
One big obstacle here is that data centers often use multiple security solutions that don't play well with one another.
"It’s crucial for organizations to integrate their security systems into a single, holistic security fabric that provides single-pane-of-glass management and visibility," John Maddison, senior VP of products and solutions at Fortinet, who’s a security expert, said. "Most data centers lack true automation due to lack of visibility. The most secure data centers are able to catch threats based on proper visibility and use automation to quarantine suspicious users."
Once AI is fully deployed in data centers, does that mean that human security experts will no longer be needed?
No, because there are still limits to what AI can do, Nick Bilogorskiy, cybersecurity strategist at Juniper Networks, said.
"The real problem is how to correctly use, interpret and make the right conclusions from it," he said. "As it stands today, this is something we still very much need a human subject-matter expert to do."
About the Author(s)
You May Also Like



.jpg?width=700&auto=webp&quality=80&disable=upscale)



