David Holmes has more than 20 years of experience in security and product engineering, and is an evangelist for F5 Networks' security solutions, with an emphasis on distributed denial of service attacks, cryptography and firewall technology. Follow David Holmes on twitter @dholmesf5.
I try to avoid doing new year industry predictions. In order to get any prediction mindshare, I have to wade pretty far out into the crazy water (“Paper currency is over!” or “This will be the year robots destroy all life!”), and the wetter I get, the less likely I am to be right. But there’s one trend from 2014 that is too important not to discuss: massive infrastructure security vulnerabilities.
In 2014, three gigantic security holes ripped through the very fabric of the Internet. These holes were so big you could drive Elon Musk’s ego through them (in your choice of a Tesla D or a SpaceX shuttle).
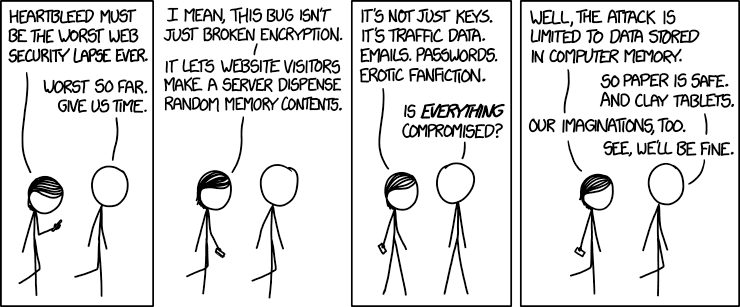
The first hole, Heartbleed, hit right in the first quarter of the year. Although CERT assigned Heartbleed only a severity 5.0, many security professionals felt that it was much worse than the rating implied. At the time, I thought it was the worst vulnerability ever: you could instruct an HTTPS server to disclose its public key? Really?
The world responded to Heartbleed with an almost gleeful urgency. Security practitioners ran around like their hair was on fire. Heartbleed was easy to socialize: not only was there exploit code, test tools, and scanners, there was also the scary name, the logo, and the T-shirts. Ivan Ristic at Qualys put up a dashboard showing the progress that the world was making toward getting Heartbleed patches deployed. Yngve Petersen at Opera continued scanning for months afterward. The Internet as a whole was patched in an amazingly short amount of time. Afterward, it was fist bumps all around (and lots of password changing).
The problem in 2014 was that we couldn’t keep up the momentum through the year.
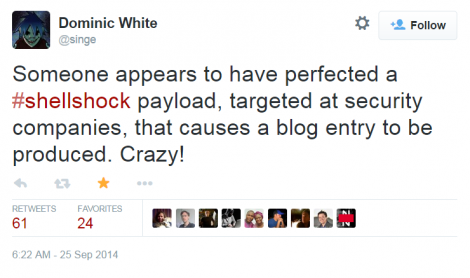
When Shellshock dropped in September, CERT gave it a severity of 10 (the highest possible). The scope of the vulnerability was breathtaking: here was a 25-year-old bug in the very heart of 60 percent of the servers on the Internet, and its reach could extend into any application that used Linux anywhere in its stack. Anything that ever piped to Bash was suspect. Yet, even though the exposure was graver than Heartbleed, there wasn’t a collective freak-out over Shellshock.
Ivan Ristic didn’t write a scanner. Yeah, there was exploit code tweeting around, but only because it was so easy to retweet. Someone put together a demo of DHCP complete ownership via DHCP, but even then, where were the scanners? Where were the dashboards? It’s as if we had expended all of our “care” bullets and we had none left. Instead, we just blogged about it. To make matters worse, RedHat flubbed its initial Shellshock patches, so eager beavers who patched early had to patch all over again.
The third security hole came at Thanksgiving, when a 19-year-old turkey called WinShock (MS14-066) allowed all Microsoft servers listening for HTTPS to be exploited remotely—and there was no workaround. If Microsoft had been feeling smug for not being vulnerable to either Heartbleed or Shellshock, they were humbled by WinShock, which CERT assigned another maximum severity. By the time WinShock dropped, even a pro security writer like yours truly was suffering from disclosure fatigue. I didn’t even have the spirit left to comment on a severity 10 vulnerability. One of our engineers wrote a mitigation script to block WinShock attempts at the load balancer. Good for him, that eager beaver. The rest of us were spent.
2014 Model of the New Normal?
What is to be learned from 2014? As we move into 2015, can the security community extrapolate on what might have simply been an outlier year?
I believe it can, but the bad news is that 2014 might be the model of the “new normal” for infrastructure vulnerabilities. Organizations are paying actual money for disclosures, which, of course, means there will be research into them. (Interestingly, the HackerOne program is building a cool new business model for this: HackerOne – it’s like Airbnb for vulnerabilities.) Also, the days of threatening security researchers with jail time for disclosure is clearly over. These two trends, however, might signal a short-term rush for more severity 10 vulnerabilities from 2015 to 2020, so get ready to be fatigued.
A Collective Sigh of Relief
The good news is that there are two new trends that should help security professionals in 2015. First, more services are getting spun up in the cloud than ever before. It turns out that, in spite of all the early hand-wringing, the cloud is proving to have some security advantages. Lately, cloud systems are enforcing stricter and stricter security policy on the images that can be spun up. And customers are getting used to these requirements (no default passwords!). With a third party—the cloud provider—scanning and auditing systems, security should be better in 2015.
Even if you’re not moving to the cloud, there’s still good news. All the work that went into patching systems and putting up dynamic defenses in 2014 will lead to fast remediation in 2015. That’s right, both for technology and for process. The industry is getting used to the idea of reducing threat surface–for example, SSL 3.0 is being wiped out due to the POODLE vulnerability. That’s a whole threat surface that has virtually disappeared. Expect to see faster and better knobs on all kinds of security devices to help you screen out the crazy stuff in 2015. Demand it from your security perimeter vendor!
Neither the cloud nor dynamic security would have prevented Heartbleed, Shellshock, and WinShock; infrastructure vulnerabilities would have emerged anyway. But, thanks to 2014, the vulnerable software can be found and patched more quickly.
It’s all well and good to look on the brighter side of life and have some optimism as the calendar turns over (gym membership, anyone?)…unless you are a security practitioner. For us, as we move into 2015, we need to be cognizant that the fabric of the Internet may be riddled with more gigantic holes just waiting for an ego to drive through them. We must stay vigilant, be ready when it happens, and not expend all our “care” bullets in the first quarter.
Industry Perspectives is a content channel at Data Center Knowledge highlighting thought leadership in the data center arena. See our guidelines and submission process for information on participating. View previously published Industry Perspectives in our Knowledge Library.