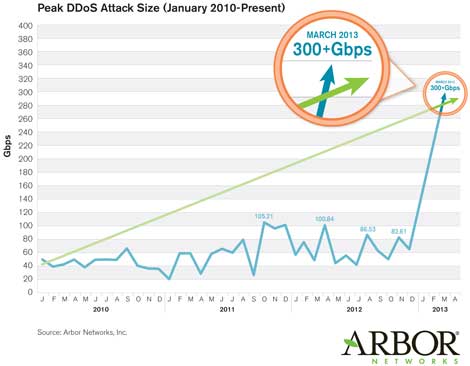
Distributed denial of service (DDoS) attacks are getting larger and more powerful.
Today’s business world is becoming ever more reliant on the data center, which has become the heart of any modern organization. With virtualization and cloud computing driving gains, many are saying that it’s a great time to be in the data center business. Although this may be the case from an infrastructure side, we can never forget that as more people move towards a platform, the bigger a target it becomes.
Here’s the real problem: Attacks against cloud providers have not only increased, they’ve also become much more sophisticated. In fact, a recent Arbor Networks report indicates that the first quarter of 2013 saw the previous record for the largest reported DDoS attack, around 100Gbps, shattered by a 300Gb/sec DNS reflection/amplification attack targeting Spamhaus. Attackers have had the technical capability to generate attacks of this magnitude for some time, and this has now been demonstrated. The attack vector used in this case was not new, as DNS reflection / amplification has been used to generate several of the largest attacks seen on the Internet in recent years. These attacks are actually relatively common, but usually at much lower traffic levels.
So, what do you do in these types of situations? A new security term has been circulating the industry. Next-generation security platforms are much more than just physical boxes sitting in the data center. Traditional means of securing a data center simply won’t cut it anymore. Standard perimeter defenses at the data center layer must be optimized to handle new types of security threats. There has been a leap in security technologies where advanced engines are doing much more deep diving than a regular firewall would.
- Virtual appliances. Many organizations are now deploying security appliances within numerous points in the data center. No longer bound by the physical aspect, virtual appliances can roam between physical hosts and have visibility into more parts of the network. Plus, they’re easier to manage from an agility perspective. Furthermore, administrators can dedicate a virtual security appliance to a specific function. This means an appliance can reside departmentally doing a certain type of service for that team. For example, Fortinet’s FortiGate Virtual Appliances create a new layer of security for a physical and virtual infrastructure. By placing these virtual appliances inside of a network, you’re able to monitor for intrusion prevention, malware, unauthorized devices, network viruses, and much more. This could prove to be much more expensive when doing something similar with a physical device.
- New scanning engines. Advanced deep scanning engines like data-loss prevention (DLP), intrusion detection/prevention services (IPS/IDS), and even device interrogation helps lock down an environment. Creating intelligent network monitoring algorithms allows administrators to control what data flows in and out of the environment. Furthermore, these new engines help control the various consumer devices that are trying to enter the environment. Security administrators can allow or prevent access from certain types of devices. In fact, they can even geo-fence their environment and prevent devices from access given an unsecure connection. Then, these devices can be interrogated, authorized and even provisioned all through secure corporate communications
- Creating layered security. The idea is to create intelligent security layers within your data center to secure the entire environment. The most important point to consider is that layers security can be logical, physical – or both. Security professionals can align necessary resouces with appropriate security measures as needed. For example, Entire applications can be placed behind intelligent, heuristic, learning engines which monitor for anomalous activity. Not only do they protect internal resources, they continuously monitor these applications against signatures based on public vulnerability databases (e.g. Snort, CVE, Bugtraq, etc.). There’s also the physical side of the security. Virtualization is certainly very cool, but what happens when you need raw throughput as well as next-generation security? Physical security appliances are now being integrated with 10Gbe cards capable of even greater amounts of expansion. You can have the best core infrastructure out there, but if your edge appliances can’t handle the throughput, you’re going to have a serious bottleneck.
Let’s face it, there are always going to be bad guys out there. Their attacks will continue to be sophisticated. However, in deploying intelligent technologies and good security practices – these attacks can be stopped at the border without really causing any damage. Cloud computing, IT consumerization and the influx of information housed within a data center has created new types of targets.
As more organizations increase their reliance on the modern data center, attack vectors will continue to evolve. Cloud and next-generation security is designed to mitigate risk above and beyond standard security measures. Remember, a good security solution not only protects your environments, it can increase your infrastructure agility as well. The future looks to leverage data center and cloud technologies even more. With mobility and the evolution of the end-user – organizations must look at new ways to secure their environment.





